Website Malware: Mobile Redirect to BaDoink Porn App Evolving
Recently, we wrote about a malware redirection on this blog where the malware was causing compromised sites to redirect their visitors to pornographic content (specifically, the BaDoink app). You can read more about what we found by going to our previous blog post.
As described in the original post, some particular files were infected (examples were the index.php, wp-config.php and others). We thought that was enough malware for one app. However, while we were working on an infected site today, we found a new malware injection causing this redirection.
Since all of the sites web files were clean and we didn’t find any suspicious Apache modules or binaries, it took a while for us to figure the problem out. However, it became much more clear once we investigated the PHP binary and found some suspicious entries.
First, after running the php -i command (which displays full php info), I got the location of the main php.ini configuration file. When I took a look at it, I saw the following suspicious entry:
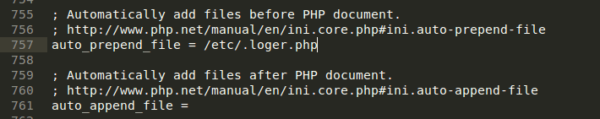
I was actually searching for the auto_append_file entry (because it is a very commonly used malware entry), but this time, auto-append was empty. Right above it, however, there was an auto_prepend_file entry that had some files assigned and it was this /etc/.loger.php, that looked very suspicious.
Here’s what we found when we opened the file:
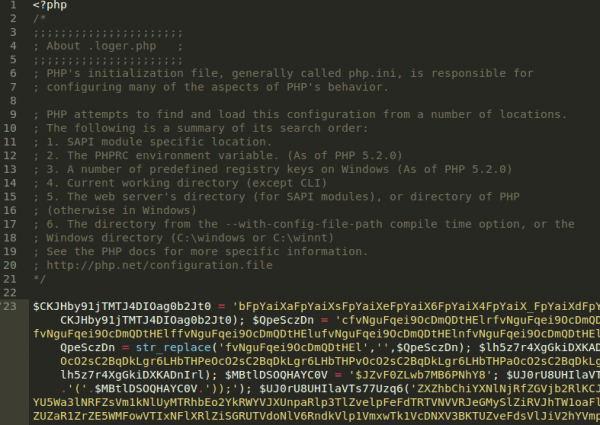
After deobfuscating it we could confirm that it was malicious and that it contained a redirection to the infamous Porn app because it used the exact same code responsible for inserting the malicious JavaScript redirects to the documents (based on the User Agent). The solution was to remove the php.ini entry, and remove the file itself, and then to restart the apache server.
Be careful because simply removing the file will cause a crash of your site and will lead to a 500 internal server error, which is why Apache needs to be restarted. However, if you want to schedule the restart for a more appropriate time, removing all of the content from this malicious file (.loger.php in this case) would do the trick and then you can remove it after restarting your apache.
What did we learn
We already knew this, but there is a lot of money to be made by redirecting website links to porn and some malicious agents will do this by hacking legitimate links and websites. In this case, there is still a lot of traffic being driven specifically to Badoink’s App. It’s important to remember that, if you hear reports of visitors being redirected and can’t get redirected yourself, your site is still at risk as much of the malware we’ve seen is conditional. Finally, if you’re having a hard time getting rid of the malware or any symptoms of malware, sign up for a plan and our team will clean your site today.
Stay safe and keep your eyes open!



No comments yet.