Malvertising on a Website Without Ads
When you first configure your website, whether it be WordPress, Joomla, Drupal, or any other flavor of the month, it is often in its purest state. Unless ofcourse the server was previously compromised, which in it of itself is another conversation outright. Barring that one instance, the new website should not exhibit any malicious behavior. Or so you would think.
It’s rare though that a default theme will satisfy your every need, it’s often has just enough to wet your beak and get you thinking of ways to extend functionality. So we set off to extend and leverage all the features our favorite CMS offer us.
Watering Down Core Security
The next steps are to add on, to extend. New themes, plugins, sliders, animated gifs, music… no, wait, that’s too 1990’s. Let’s focus on themes, plugins, templates and various other extensions found in today’s modern CMS applications.
Often, the first thing you have in mind when choosing anything for your website is functionality and aesthetics, right? We all want something that looks great and improves user experience. It may be a really cool theme or the newest social network plugin; it’s not a common practice however to inspect its behavior.
What if one of the add-ons you installed is injecting hidden ads on your site? Or what if they are loading pop-up windows like this one?
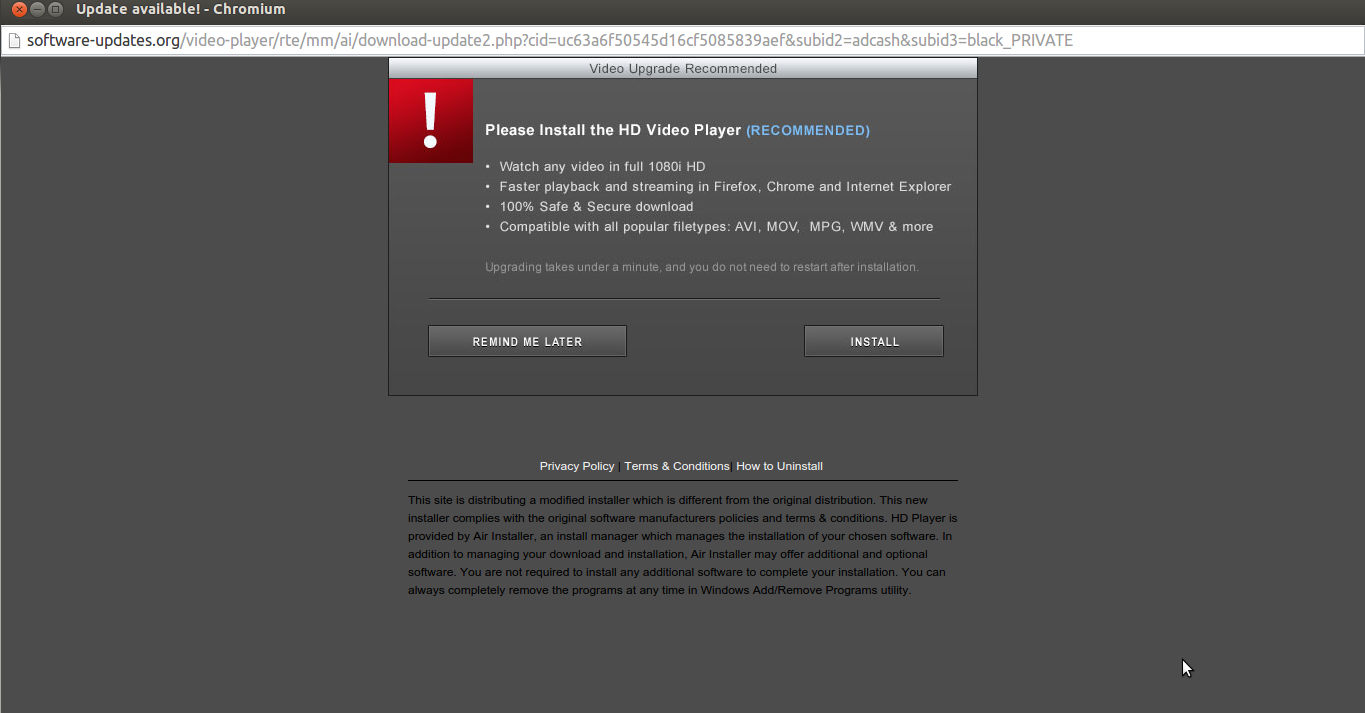
Malicious Fake Flash Download
This is exactly what a client recently experienced. After installing a clean install of their CMS, configuring and extending it with a new theme, their website started to present it’s users with a Flash installer. For those wondering, this is fairly common, and is something known as a Drive-by-Download. More on that another time though.
Following The Trail
As is natural for us in the research group we can’t help but get lost in cookie trails, every crumbs proves to be more fascinating than that last.
While investigating, it became apparent that the Flash installer was being loaded via an ad, an ad that was being served via an ad network. Immediately I’m thinking malvertising, right?
In this case, the owner hadn’t configured advertising though and yet it was loading content from an ad network.
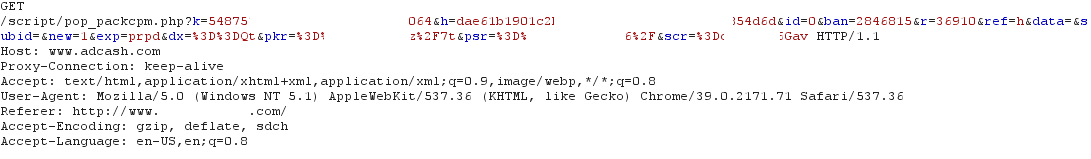
For your reference, here’s the HTTP Request showing the ad was being loaded by the infected website.
While investigating the code I couldn’t find any reference to the adcash.com domain in either the theme or plugin files. Again, the website owner confirmed that he was not using any ad networks. So that left us no choice but to dig a little deeper, we started to investigate the HTTP traffic.
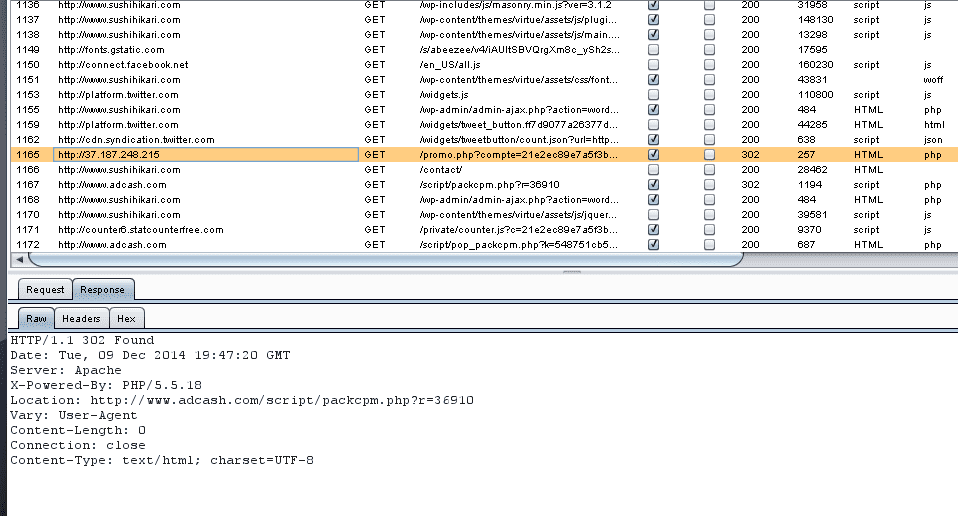
While intercepting the sites Requests and Responses I came across the following entry:
It’s a request to hxxp:// 37.187.248.215 that returned a 302 Redirect to adcash.com. Yes, success!!! All right! We are one step closer to the source, I was probably looking for the wrong URL in the source code. Duh… Address noted, let’s keep checking the HTTP traffic.
Checking the HTTP responses for that IP address I found this:
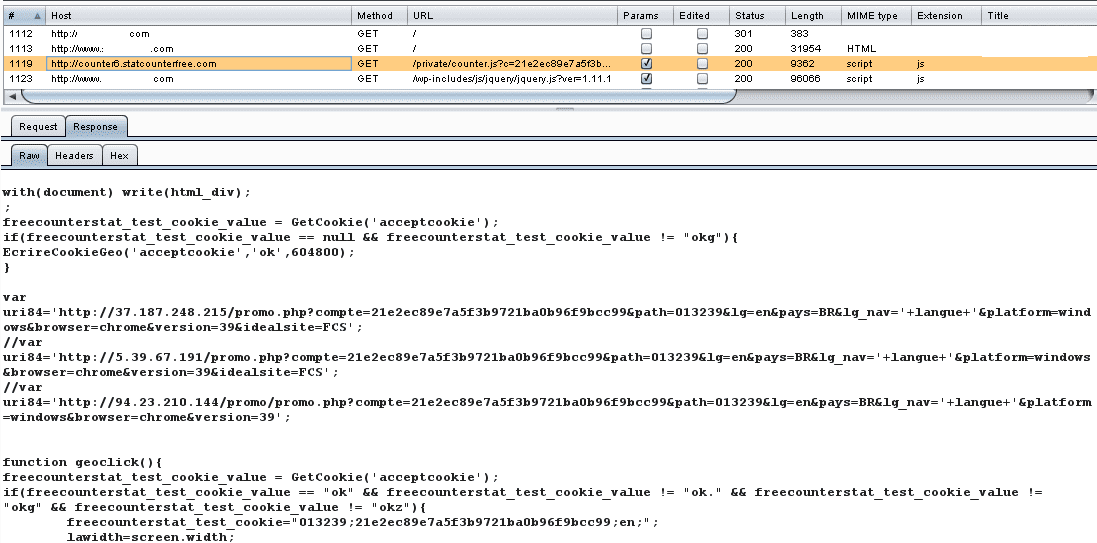
URL Variable in HTTP Headers
There it is, the hit counter JavaScript code was loading the ad, as you can see the URL in the uri84 variable. It is making a request here: counter6.statcounterfree.com. This request was causing the popup, but was only being triggered once per visitor and the content looks random, suspicious and, more importantly, unwanted.
Adware or Malvertising?
Turns out that the client did in fact add the counter script to their themes footer, so it didn’t come prepackaged. They were trying to keep track of their visitors, they had no intentions of their site being used to serve ads though.
So being that the source of the counter was www.freecounterstat.com I decided to spend some time familiarizing myself with what they do. I spent some time reading through their End User License Agreement (EULA), you never know what goodness you agree too.
Unfortunately, no luck, nothing related to terms or privacy on the website. So I contacted their support to see if this type of behavior was expected.
Based on their response, I’d argue it probably wasn’t:
Hi,
I turn off popup on your account
chris
This is the message I received from support. There are obviously a number of things with that response that worry me, but now the clients website is clean. Whether intentional or not, it’s hard to say, but I’d likely categorize it as a compromised ad network and a malvertising attack.
Personally, I’d stop using this counter script. It’s obviously very 1990 for one, but more importantly if the solution is to disable ads for this site, but not address the bigger issue of drive by downloads being used via the service, that is very concerning. We’ve written about the dangers third-party scripts and service introduce to your environment, this is another example of that.
Conclusion
It is really hard to keep an online service, and even harder if you are doing this for free, so it is understandable that a service uses the adware model to maintain itself. However, it must disclose this to it’s users and offer them an option to opt out. To do it and not offer a user this options is wrong, and as website owners you must be more diligent.
Always check the terms, EULA and privacy policies of third-party software you are using on your website. If they don’t have them, that’s probably a good sign not to use them. Look for any suspicious terms before agreeing to them. If you need help, or you suspect that a plugin or theme is behaving maliciously, let us know.
We love looking through code and potential issues…:) Hit us up at [email protected]. Happy hunting!!



No comments yet.