Website Malware – Mobile Redirect to BaDoink Porn App
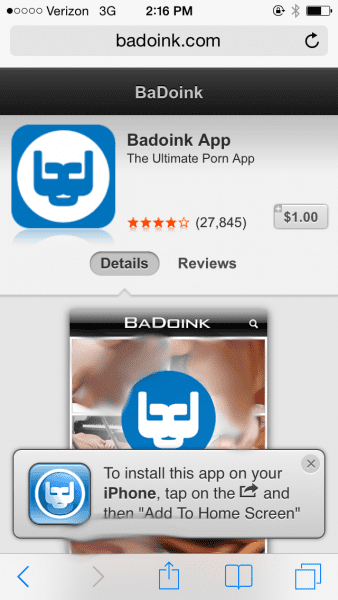
A few weeks ago we reported that we were seeing a huge increase in the number of web sites compromised with a hidden redirection to pornographic content. It was a very tricky injection, with the redirection happening only once per day per IP address and only if the visitor was using a mobile device (IPhone, Android and a few others).
These types of injections are called conditional redirections because certain conditions need to be met for them to redirect visitors. They are not always present and the malware authors try very hard to hide them from the website owner. The malware code looks for logged in cookies to try to identify whether or not someone is managing the site and then attempts to never redirect someone who is logged in. Finally, if a visitor gets redirected once, the malware will not redirect them again. The goal for the malware author is for visitors to not report something going wrong with a website. In this example, if you were to visit an infected site, you’d be redirected, but from your point of view, maybe it was just something weird so you retype the url and now you aren’t redirected. Since everything is working normally now, you decide not to report it and the malware lives on.
As you can imagine, this sort of malware can be difficult to troubleshoot. In fact, very often webmasters think it’s a typo and move on instead of investigating what happened. For that reason, most sites remain compromised, so if anyone ever complains that your site redirecting to “instabang.com” or a Badoink Porn App, it is very likely your site is hacked.
For more details on our previous analysis, you can visit our previous post, about malicious redirections to porn websites on mobile devices
Technical Analysis – New range of injections
Initially, this injection was happening through hidden forms that were automatically submitted via javascript upon page load. This last version of the malware has been modified. Now, it’s using javascript to force a redirection to a secondary landing page. This is the javascript code:
top.location.replace(“httx://www.1strateannuities.com/199c99c6d718c7b222eaa1a5fabd2467.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102″);
As you can see, it uses “top.location.replace” to send the user to another compromised domain (in the case above 1strateannuities.com), where it then sends the user to http://ads.mobiteasy.com/mr/?id=SRV0102.
Once there, it decides where to redirect the user, which is often to either the BaDoink porn app or to instabang. Just in the last few days, these were the sites misused as the initial redirection vector:
http://www.1strateannuities.com/199c99c6d718c7b222eaa1a5fabd2467.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102"); http://www.1strateannuities.com/199c99c6d718c7b222eaa1a5fabd2467.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://www.2013foundations.com/22ab9c9bdeae7b074719eca789ea3397.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://medicalhospitalitygroup.com/28d8e465d7d573b25255f5d56750faef.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://www.10dayssold.com/3615ccfb9d6365cf44b9b34a941ccaf4.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://www.10k-cash.com/3f7c4df28646c8fd08285cfbd8ba3cee.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://sifamuk.com/f3d61b9cc0e63a87dccf63754bdd2dd6.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://www.10dayweightlosschallenge.com/276f2bb01190a423ec7b9ca7d8e9fad0.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://robbiehoucek.com/83b028352b34c11fb2cddff566c9fd8a.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://urbanincubation.com/d275d964cd71fc4c8f0963450b6958a0.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102http://testx2.vladogeorgiev.com/7a9ca9045edbb37f0eaa13cd3f6071d0.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://knoxvillewaterfirerestoration.com/3cef451625a50c08bff223372895dd33.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://sorianoproperties.com/22ffc02b577e6d1fa21813e208417d14.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://riverstonefitness.com/ca785b5cbf87edf65e02423cb2d36e67.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://sportsbettorz.com/4c9269300f2a7ed6c8e7a1db7f7cae09.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://roofingservicesct.com/489219955adc40fc371fc60d230cc583.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://pinkyoda.com/f8c07d6deddf8d43360860efa140da44.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102 http://quemooono.com/8c6d28f83c82058736543b0cb6905045.php?s=http://ads.mobiteasy.com/mr/?id=SRV0102
Removing the Porn Redirection
Shameless Plug: If you have used SiteCheck and notice the issue I mentioned above – showing dirty then clean or not showing at all – have no fear, this does happen from time to time. It’s how the scanner works. Rest assured though, our team is able to address the issue and our internal scanners will catch the issue outright once configured.
If you’re not sure if you’ve been hacked, we’d recommend asking a couple of friends, who aren’t affiliated with your site and haven’t visited it in a while, to visit your url. As well, make sure you understand the symptoms of malware. In this case, if something feels off, then something is probably wrong and your site could be at risk. If that’s the case, our team can help.
To address the issue yourself, make sure to investigate in these locations:
- /index.php
- /wp-config.php (if using WordPRess)
- /configuration.php (if using Joomla)
- /wp-content/themes/yourtheme/functions.php (if using WordPress)
These are the 4 places where we see this injection being added. Note that it is highly encoded, and that you will have to look for any line that looks out of place. In most cases, it’s probably best to engage your developer for help.
Remember, the issue at the surface – the infection – is only the tip of the iceberg. If your website is infected you have to assume that the attackers have penetrated your defenses and have added controls that will allow them to continue to penetrate your environment so be sure to look for backdoors.
If you’re sick of reading about new malware incursions every single week, just know that there is money for the bad guys in malware of all kinds. You can protect your site from hard to detect problems, like conditional redirects, without ever having to worry that you’ve been attacked by adding firewall protection, like our own CloudProxy Firewall.
If you have any questions about this redirect or anything else, let us know. You can also engage us on Twitter at Sucuri Security or Sucuri Labs.



No comments yet.